By: Syamilah Yusman and Farzana Rozaidee
In an era where the nation’s heartbeat is synchronized with digital networks, the line between national security and personal privacy has grown increasingly thin.
As Malaysia navigates its path as a digital-first economy, the shadows of the web have birthed sophisticated threats that target the very core of our society.
At the front lines of this invisible war is CyberSecurity Malaysia (CSM). Through its specialized Cyber999 unit, CSM has evolved from a technical support center into a critical pillar of public safety, orchestrating a complex defense against data breaches, AI-driven fraud, and infrastructure sabotage.
The Surge of the “Silent Pandemic”
The year 2025 marked a sobering turning point for Malaysia’s digital landscape.
According to a specialist and log analyst at Cyber999, Kilausuria Abdullah, describes the current state of cybercrime as “serious.”
“The transition from 2022 to 2025 saw an unprecedented escalation in risk, while only 50 cases of data leaks were recorded in 2022, that number skyrocketed to 562 cases by November 2025,” she said during the interview.
This surge is largely attributed to the industrialization of cybercrime.
“Attackers now deploy ‘infostealers’, malicious software designed to harvest passwords and banking information from browser autofill data,” she added.
These infostealers allow them to bypass traditional security using a victim’s own valid credentials.
Furthermore, high-profile incidents like the KLIA ransomware attack in March 2025 and the Maybank data leaks have demonstrated that hackers are no longer just targeting individuals, but they are aiming for the National Critical Information Infrastructure (NCII).
As Kilausuria warns, the government will be paralyzed if these cases result in a high impact.
Technical Fortification and The AI Frontier
Kilausuria stated that to counter a threat that moves at the speed of light, CSM has shifted toward a proactive, AI-driven defense model.
Supported by the National Artificial Intelligence Office (NAIO), the organization now utilizes Adaptive AI to predict and intercept attacks before they can infiltrate sensitive systems.
“The defense architecture is built on three technical pillars, the first is Security Information Management (SIM). This system uses live log correlation to collect and analyze data from every device on a network, displaying instant alerts upon detecting cybercrime.
“Next is Security Orchestration, Automation, and Response (SOAR). It can be used when a threat is detected, SOAR triggers immediate containment protocols, effectively ‘quarantining’ the malware to prevent it from spreading,” she said.
Last but not least, the Cybertrack Platform, a collaborative tool, allows for the real-time sharing of Tactics, Techniques, and Procedures (TTPs), ensuring that a threat identified in one sector can be defended against in all others.
Legislation: A New Era of Accountability
As technology evolves, the legal shield protecting Malaysians has undergone a radical transformation.
The government’s commitment to holding organizations accountable is most visible in the Personal Data Protection Act (PDPA).
To deter negligence, penalties for data breaches have been severely increased from RM300,000 to a maximum of RM1 million, coupled with potential three-year prison sentences.
Furthermore, Malaysia is preparing to lead the region with a dedicated AI Governance Bill set for June 2026.
This legislation aims to regulate the ethical use of AI and provides a specific legal framework to prosecute those who use “deepfake” technology for extortion and impersonation.
The Human Element: Strengthening the Weakest Link
Despite the high-tech sensors and million-ringgit fines, Kilausuria maintains that “the weakest link is the human.”
With over 34.9 million internet users, the surface area for social engineering is vast.
Attackers now use AI to generate “hyper-localized” phishing content that mimics the exact tone of the PDRM or LHDN, tricking even cautious users into revealing their Personally Identifiable Information (PII).
To bridge this gap, Kilausuria advocates for a “Golden Hour” response and proactive digital hygiene.
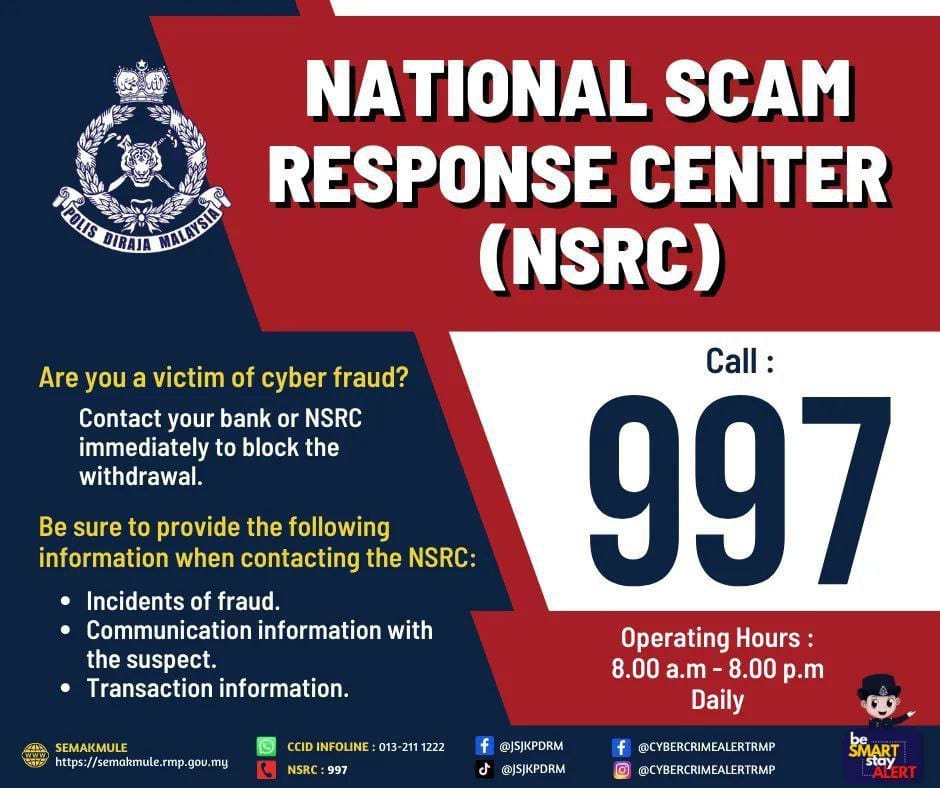
“Victims of scams are urged to contact the National Scam Response Centre (NSRC) at 997 within one hour of an incident to maximize the chances of freezing stolen funds,” she said.
On an individual level, the implementation of Multi-Factor Authentication (MFA) and tools like ‘Have I Been Pwned’ (HIBP) remain the most effective forms of personal defense.
Sources: twitter
https://x.com/JaPenWPKL/status/1603568632126001152/photo/4
CONCLUSION
The role of CyberSecurity Malaysia has shifted from merely “fixing computers” to protecting the sovereignty of the nation’s data.
While the 2025 to 2026 landscape presents a “rising tide” of sophisticated threats, the combination of AI-driven tools, stringent new laws, and a more vigilant public offers a path toward digital resilience.
In this new era, cybersecurity is not just a technical requirement, it is a shared national responsibility.

